How It Works
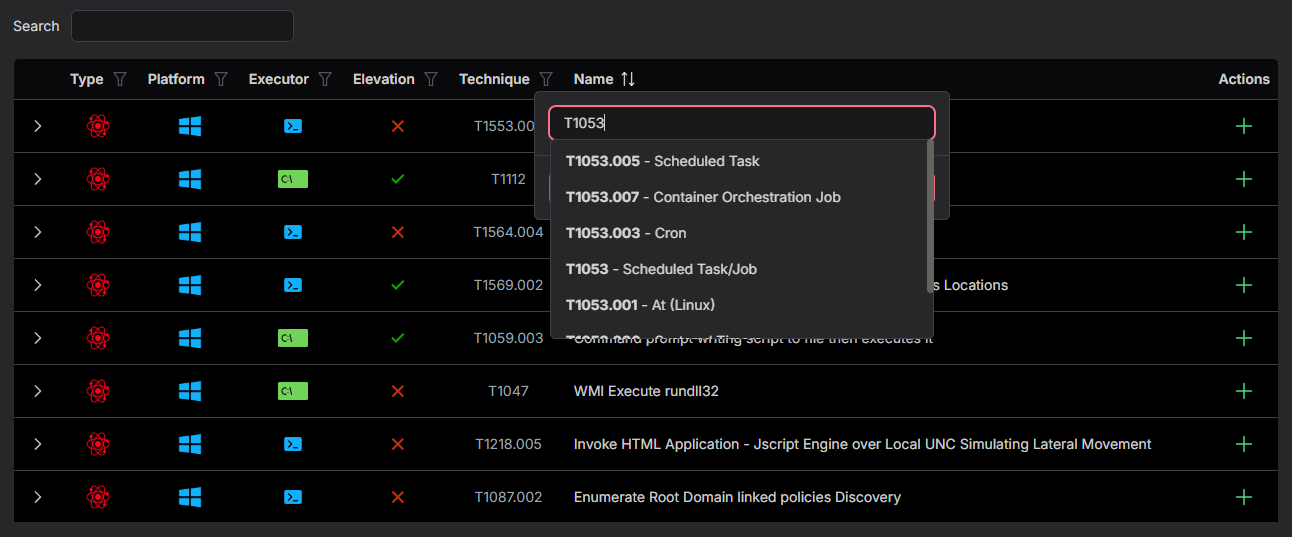
- 1. Browse — Search and filter thousands of adversary procedures by tactic, technique, platform, or keyword
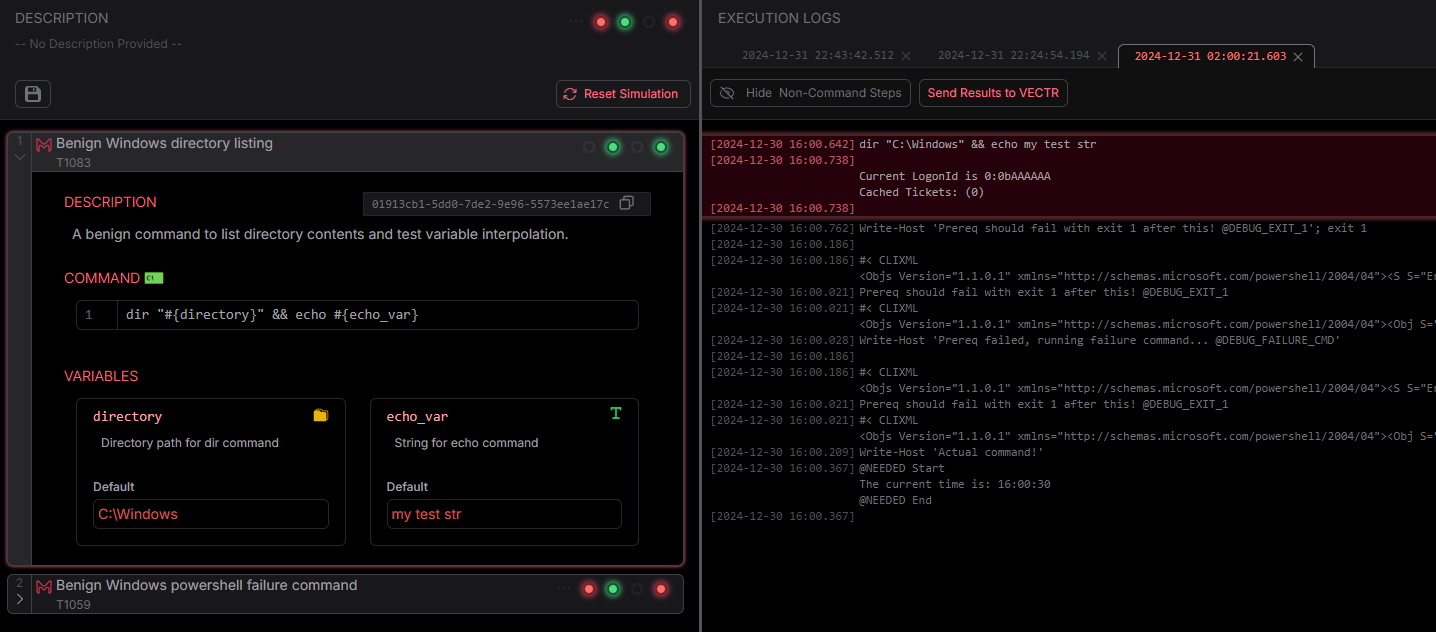
- 2. Build — Add procedures to a simulation and configure arguments for your environment
- 3. Run — Execute across PowerShell, CMD, Bash, or Sh with real-time status
- 4. Review — Check detailed per-step logs and send results to tracking tools
Feature Overview
| Name | Availability | |
|---|---|---|
| Get Started Immediately | ||
| Thousands of adversary procedures synced automatically from Atomic Red Team | ✔️ | |
| MITRE ATT&CK tactics and techniques mapped to every procedure | ✔️ | |
| No infrastructure, agents, or setup required | ✔️ | |
| Build Your Own | ||
| Create custom procedures with your own steps, arguments, and variables | ✔️ | |
| Execute Across Environments | ||
| Run procedures via PowerShell, CMD, Bash, and Sh | ✔️ | |
| Windows 10/11 and macOS supported | ✔️ | |
| Track What Happened | ||
| Detailed execution logs with per-step results | ✔️ | |
| Send results directly to VECTR via API | ✔️ | |
| Pick up where you left off with sessions that save automatically | ✔️ | |
| Share With Your Team | ||
| Save and load simulations as human-readable TOML files | ✔️ | |
| Import Atomic Red Team YAML directly | ✔️ | |
| Attach files to procedures and package everything as portable archives | ✔️ | |
Feature Details
Get Started Immediately
MACAT syncs Atomic Red Team procedures and MITRE ATT&CK data automatically on first launch. Filter by tactic, technique, platform, or keyword to find exactly what you need.
Track What Happened
Every procedure step is logged with its command, output, and result. Review what ran, what succeeded, and what failed. Send results to tracking tools like VECTR to measure progress over time.
Share With Your Team
Save simulations as human-readable TOML files. Import Atomic Red Team YAML directly. Attach files to procedures and package everything as portable archives.